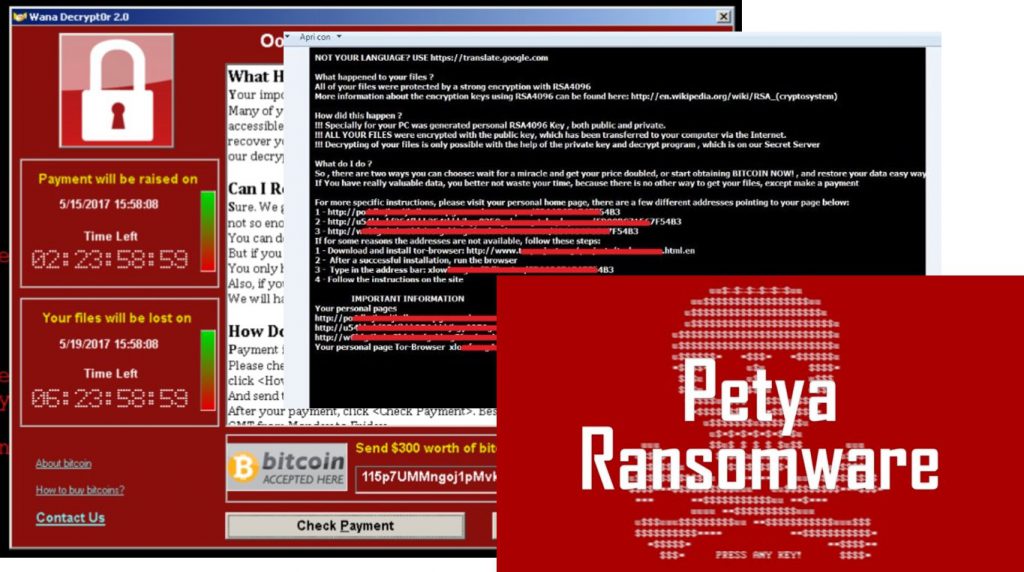
There has been widespread talk in the press about the damage caused by recent ransomware attacks (Wannacry, NotPethya, etc.): are there any confirmed figures in the industrial world?
Answer: it is always difficult to have numbers in these cases.
A few months ago we published a “report” of our misadventure with Cryptolocker, the "father" of Pethya-nonPethya, which in our case had a very marginal impact thanks to the preventive defenses applied: an hour and we had everything available and working again, even if others were not so lucky (or good? ).
In an office (or IT) environment, calculating damages is not easy because several variables must be considered: how long is the office closed? Have I lost sensitive data? What is the image damage?
In an industrial environment, these variables are combined with a certain reluctance to admit and therefore knowing what damage has been caused by the latest wave of the virus is practically impossible.
All true but some data has circulated...examples? read below…
- The British consumer products company Reckitt Benckiser (some brands: Calinda, Calfort, Finish, Clearasil, Durex, Glassex, Woolite, Veet, Sole-MiraLanza, Napisan, Nurofen, Marigold, etc.), has suffered a production disruption that is expected could equate to £110m ($135 million) or 1% of annual global sales : “Consequently, we were unable to ship and invoice some orders to customers prior to the close of the quarter,” the British consumer goods company said in a statement on Thursday. “Some of our factories are currently still not operating normally but plans are in place to return to full operation.” https://www.theguardian.com/business/2017/jul/06/cyber-attack-nurofen-durex-reckitt-benckiser-petya-ransomware
- The Danish shipping company Maersk (cargo leader and largest owner of merchant ships in the world https://it.wikipedia.org/wiki/Maersk ) damages of $300M https://www.porttechnology.org/news/maersk_fights_shipping_backlog_caused_by_petya_cyber_attack
- Saint Gobain, https://it.wikipedia.org/wiki/Saint-Gobain one of the largest glass producers in the world 200M€ (http://www.thehindubusinessline.com/companies/petyahit-saintgobain-says-its-gst-ready/article9743769.ece )
- Merck, Bio-Farma Giant (drugs and vaccines) “Merck reported it still has not fully quantified the financial impact NotPetya had, but said the malware's impact has compromised the company's ability to fulfill some orders in specific, unnamed, markets. This news was released in the company's second quarter financial release.”http://www.healthcareitnews.com/news/petya-cyberattack-halts-merck-production-hurts-profits
- Mondelez (world's largest producer of snacks and chocolate Milka, Oreo, Cadbury, Halls, Carte Noire, etc.): -3% of Q2 sales (they failed to invoice at the end of Q2). http://securityaffairs.co/wordpress/60782/cyber-crime/mondelez-international-cyber-attack.html
- Renault-Nissan, plant shutdowns and lack of production for a week in 5 plants http://www.businessinsider.com/renault-nissan-production-halt-wannacry-ransomeware-attack-2017-5?IR=T
- Russian oil company Rosneft (also partners in Pirelli) 2“The company's servers underwent a powerful hacking attack,” the company said on Twitter. “The hacking attack could lead to serious consequences, but the company has moved to a reserve production processing system and neither oil output nor refining have been stopped.” https://www.reuters.com/article/us-russia-rosneft-cyberattack/russias-rosneft-says-hit-by-cyber-attack-oil-production-unaffected-idUSKBN19I1N9
- Fedex (“FedEx reported the damage from Petya will likely be permanent,”) The difficulty could reduce FedEx's earnings by 50 cents to $1 a share for the year through next May, Citigroup Inc. analyst Christian Wetherbee said in a note. That represents 4 percent to 7 percent of the $13.50 he estimated for earnings.
We will talk about this (and above all the solutions to be applied) at the ASSINTEL WEBINAR on 13 October (registration and free participation).
Some more info:
The Assintel Working Group on IT Security gives voice to Francesco Tieghi and Enzo Maria Tieghi on the occasion of the series of webinars organized to rattle off the various aspects of the CyberSecurity issue in the IoT era.
New issues, the Security by Design approach, existing and upcoming regulations: these are the points that will be touched upon in the webinar on Wednesday 13 September.
complete program and registration at the links below.
INTRO:
Almost all industrial supervision and control systems (ICS) are connected to the company network, sometimes unconsciously and without effective control. It is easy to understand how problems that arise outside the "plant floor" can have repercussions on the process and vice versa: line PLCs and PCs can become "back doors" and create problems on the upper floors.
Topics Covered
In this webinar we intend to consider the different facets of Industrial Cyber Security following the agenda below:
- Introduction to industrial cyber security
- Differences Safety and Security, ICS/SCADA Security
- Security in ICT environments and industrial/utility environments
- Terminology, scenarios and technologies, why and how to protect plants
- Threats and vulnerabilities of control systems
- Segmentation of networks and segregation of control systems
- Zoning & Conduit, according to ISA99/IEC62443
- Consolidation, virtualization and Cloud in control and remote control environments
To subscribe
Click here to register on the platform.
The initiative is reserved for Assintel Members and is free.
Not a member? You can request us to participate in the webinar by sending us an email to the following address segreteria@assintel.it
The webinar cycle
See other dates and topics clicking here